Main Highlights:
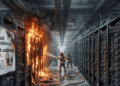
- Saturday night, attackers stole hundreds of NFTs from OpenSea users, causing concern among the site’s enormous user base.
- According to a spreadsheet provided by PeckShield, the attack resulted in the theft of 254 tokens, including those belonging to Decentraland and Bored Ape Yacht Club.
- The attack appears to have exploited a vulnerability in the Wyvern Protocol, an open-source standard that enables most NFT intelligent contracts, including those built on OpenSea.
- On Twitter just before 3 a.m. ET, OpenSea CEO Devin Finzer indicated that the attacks did not originate from the business’s website, its listing systems, or any emails issued by the company.
- The campaign’s quickness – hundreds of transactions in a matter of hours — suggests a similar vector of attack, albeit no connection has been discovered thus far. The campaign’s quickness – hundreds of transactions in a matter of hours — suggests a similar vector of attack, albeit no connection has been discovered thus far.
On Saturday, attackers stole hundreds of NFTs from OpenSea users, generating panic among the site’s large user base late at night. According to a spreadsheet created by PeckShield, 254 tokens were taken during the hack, including tickets from Decentraland and Bored Ape Yacht Club. The majority of the assaults occurred between 5 and 8 p.m. ET and targeted a total of 32 people. Molly White, the blogger behind Web3, is Going Great, said the stolen tokens were worth more than $1.7 million.
The assault appears to have taken advantage of a weakness in the Wyvern Protocol. This standard open-source powers most NFT intelligent contracts, including those built on OpenSea. According to one theory (shared on Twitter by CEO Devin Finzer), the assault occurred in two stages: first, targets signed a partial contract with a generic authorization, and significant sections were left blank. With the signature in place, attackers completed the arrangement by calling their agreement, which automatically transferred the NFTs.
In essence, the targets of the assault signed a blank check — and once signed, attackers completed the assessment to seize their assets. The user, who goes by the handle Neso, stated that he verified each transaction. They all have genuine signatures from the individuals who lost NFTs; therefore, anybody claiming they were not phished but did lose NFTs is, unfortunately, incorrect.
OpenSea has grown to be one of the most valuable firms of the NFT boom, valued at $13 billion in a recent fundraising round, by offering a straightforward interface for users to list, explore, and bid on tokens without dealing directly with the blockchain. This success has been accompanied by considerable security concerns, as the business has battled assaults that used outdated contracts or poisoned tokens to steal customers’ precious holdings.

When the assault occurred, OpenSea modernized its contract system, although OpenSea has disputed that the attack began with the new contracts. Due to the tiny number of targets, such a vulnerability is improbable, as any fault in the broader platform would almost certainly be exploited on a far larger scale.
Numerous specifics of the assault remain unknown, most notably how attackers convinced the victim to sign the half-filled contract. OpenSea CEO Devin Finzer stated soon before 3 a.m. ET on Twitter that the assaults did not come from the firm’s website, different listing systems, or any emails sent by the company. The campaign’s rapidity – hundreds of transactions in a couple of hours — implies a similar attack vector, although no relationship has been established thus far.
About NFTs
“Non-fungible” essentially indicates that it is unique and cannot be substituted by another item. For instance, a bitcoin is fungible; exchange one for another, and you’ll have the identical item. However, a one-of-a-kind trade card is not fungible. If you swapped it for another card, you’d end up with something entirely different.